The Agents in Night’s Black Agents are burned spies, out of favour with their former agencies, banished into the cold – but even a broken spy has uses. Smiley got called back from retirement all the time; unsanctioned operations call for unsanctioned assets. What sort of unofficial intel ops might your Agents get involved in […]
Tag Archives: night’s black agents
I’ve been running a mini-series of Night’s Black Agents – the third season since I started the game. This post describes game prep. The team have a vampire encased in a block of concrete which they kept in a silo in the Crimea – but the Russians invaded, so they moved the body and the […]
“The last conscious effort which imagination made was to show me a livid white face bending over me out of the mist. I must be careful of such dreams, for they would unseat one’s reason if there were too much of them.” — Mina Harker’s journal, 1 October (26 July 1894) Dracula isn’t the only […]
In the latest episode of their entirely authentic podcast, Ken and Robin talk combining The Esoterrorists with Night’s Black Agents, Krazy Kat in the dreamlands, the Beardmore Viking Hoax, and Happy Science.
In the latest episode of their double fun podcast, Ken and Robin talk doppelganger One-2-One, Night’s Black Agents in Asia, multiverses in the zeitgeist, and Eugene of Savoy.
In the latest episode of their self-explanatory podcast, Ken and Robin talk WhatIsThis plot hooks, Arminius Vambery, categories of fictional characters, and Soviets on the moon.
Dracula Daily emails you once a day with the text of whatever elements of (the redacted) Dracula happened on that date. So, a day’s email might be a single entry from Jonathan Harker’s diary, or some pieces of correspondence between Lucy’s suitors. Or nothing at all, if no letters or diary entries are dated that […]
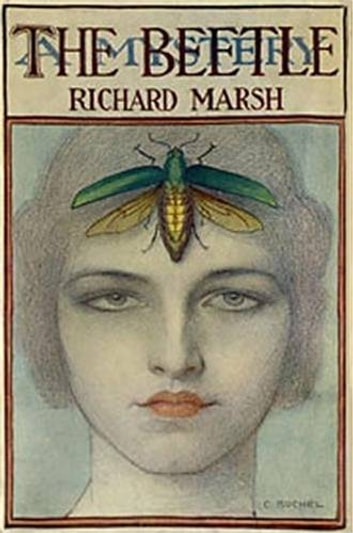
“As he replied to my mocking allusion to the beetle by echoing my own words, he vanished, — or, rather, I saw him taking a different shape before my eyes. His loose draperies all fell off him, and, as they were in the very act of falling, there issued, or there seemed to issue out […]
For some time now, the Agents have been on the trail of something called FOREVER. From what they’ve gathered, FOREVER is some sort of vampire-connected program run by shadowy elements within the United States intelligence community. Some claim FOREVER’s an ultrablack operation, a dozen levels higher and deeper than anything at Groom Lake. Other accounts […]
In the latest episode of their virtually priceless podcast, Ken and Robin talk Fall of DELTA GREEN meets Night’s Black Agents in Cambodia, penultimate horror essentials, NFTs of Carcosa, and saving Will Rogers.